About Us
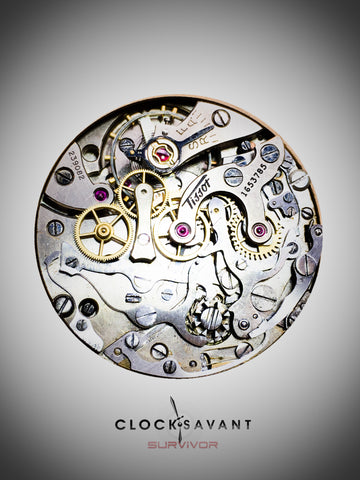
Mechanical watches and clocks convey the art, science, engineering, and history of our culture, guiding us through the passage of time, and marking the progression of our lives from generation to generation. They tell time by using the energy from our very being and give it back with precision and beauty. My name is Eric Greenberg and ClockSavant represents the culmination of my obsession with time, spanning a period of over 25 years.

As a collector, watchmaker, and clockmaker, I have crafted this company to combine the best of everything horological for the benefit of our customers. This website, the services we provide, and timepieces we offer maximize the joy of quality mechanical watches and clocks, the history of past generations, the sharing of mechanical timekeeping with future generations, and are intended to provide education, trust, and assurance in our offerings.
Eric Greenberg is the founder of ClockSavant and is a horologist, watchmaker, and clockmaker. ClockSavant services and timepieces maximize the joy of quality mechanical watches and clocks, the history of past generations, and the sharing of mechanical timekeeping with future generations. ClockSavant represents Eric Greenberg’s obsession with mechanical timekeeping spanning more than 20 years. Prior to ClockSavant, Eric had a long career in information security, networking, and IT. Eric Greenberg founded Cloud Approach, a company dedicated to thought leadership and innovation in the delivery of cloud computing and virtualization strategy, security, and implementation services and toolsets. He has more than 30 years of groundbreaking Internet, security and IT experience as an executive, author, and consultant. Eric served as SVP of Security and Risk Solutions at Integralis where he led innovation and significant new business growth. During his tenure, Integralis was successfully acquired by NTT Communications. Highlights of Eric’s career include his role at Netscape where he led their security group managing the deployment of a range of pioneering technologies including the one used for nearly all security on the Internet today, the Secure Sockets Layer (SSL/TLS) protocol. At a key time in the growth of the Internet, as Director of Engineering for Global SprintLink, Eric led the design and deployment of one of the largest international Internet networks of its time. He also served as VP of IT Global Services at the Discovery Channel.
Eric is the author of two widely read books, Mission Critical Security Planner and Network Application Frameworks, and served as a member of the editorial board for the journal of Computers & Security, United Nations International Federation for Information Processing. He holds a Master’s degree in Electrical Engineering from Cornell University and a Bachelor’s degree in Electrical Engineering from the University of Maryland.
Please spend time exploring our website and contact us with any questions or comments. We look forward to sharing our passion for time with you.
We are a member of the American Watchmaker Clockmaker Institute (AWCI). We accept all major credit cards, wire transfer, and PayPal.